Protect your mission-critical SAP landscapes from within. Experience the industry’s most established platform, embedded in the application layer to defend your core from the inside out. No external servers. No agents. Just proven defense for S/4HANA and SAP RISE.
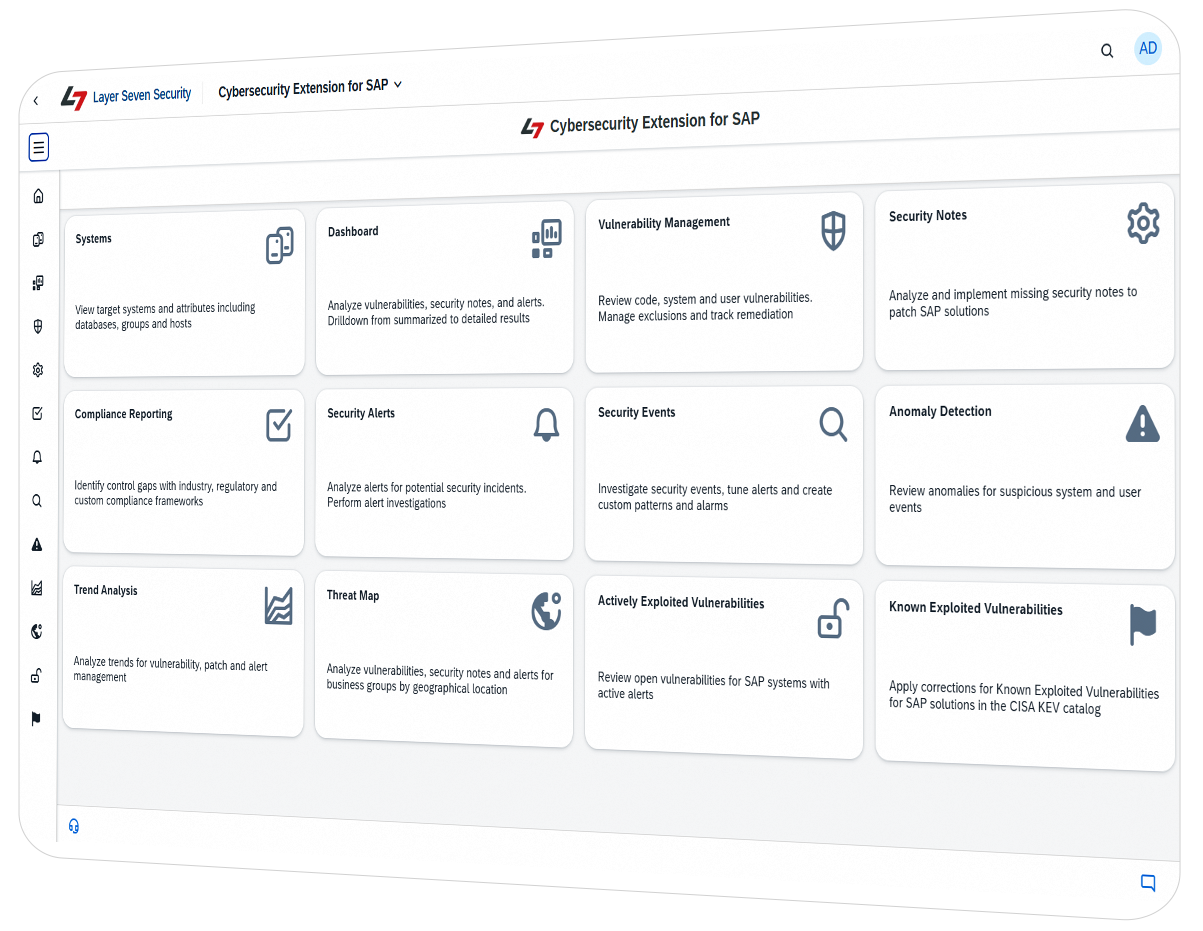
Mitigate board-level risk and automate evidence collection for NIS2, SOX, and GDPR. Simplify compliance audits for SAP RISE and Cloud ERP.
Engineered for rapid deployment and low maintenance. Deploy our SAP-certified addon in just 6 hours without additional infrastructure and overhead.

























As one of the industry’s most established SAP security specialists, we provide the deep-stack protection for SAP solutions that generic security tools simply cannot match.
Protect your mission-critical systems from within. Unlike generic security tools that secure the perimeter or underlying hosts, our SAP-certified platform is embedded directly in the application layer to defend your SAP landscape from the inside out.
By operating from the within your SAP systems, we eliminate the blind spots that external scanners miss with zero infrastructure tax.
Trust an SAP partner that has been securing SAP systems for over 15 years
Secure application, database and host layers in SAP systems for end-to-end protection
Deploy as an ABAP addon in just 6 hours without any additional hardware or agents
Protect against advanced persistent threats including cybercrime and state-sponsored attacks.
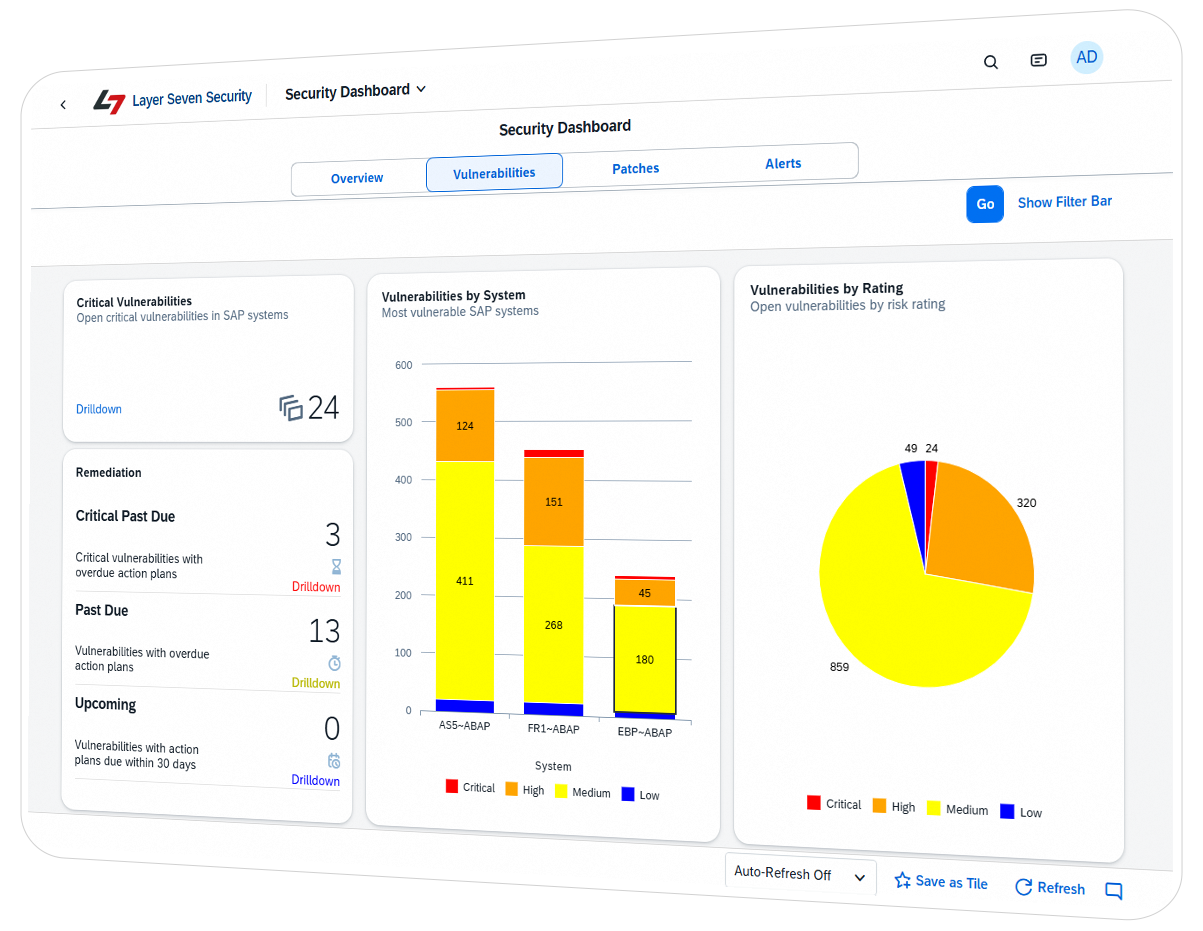
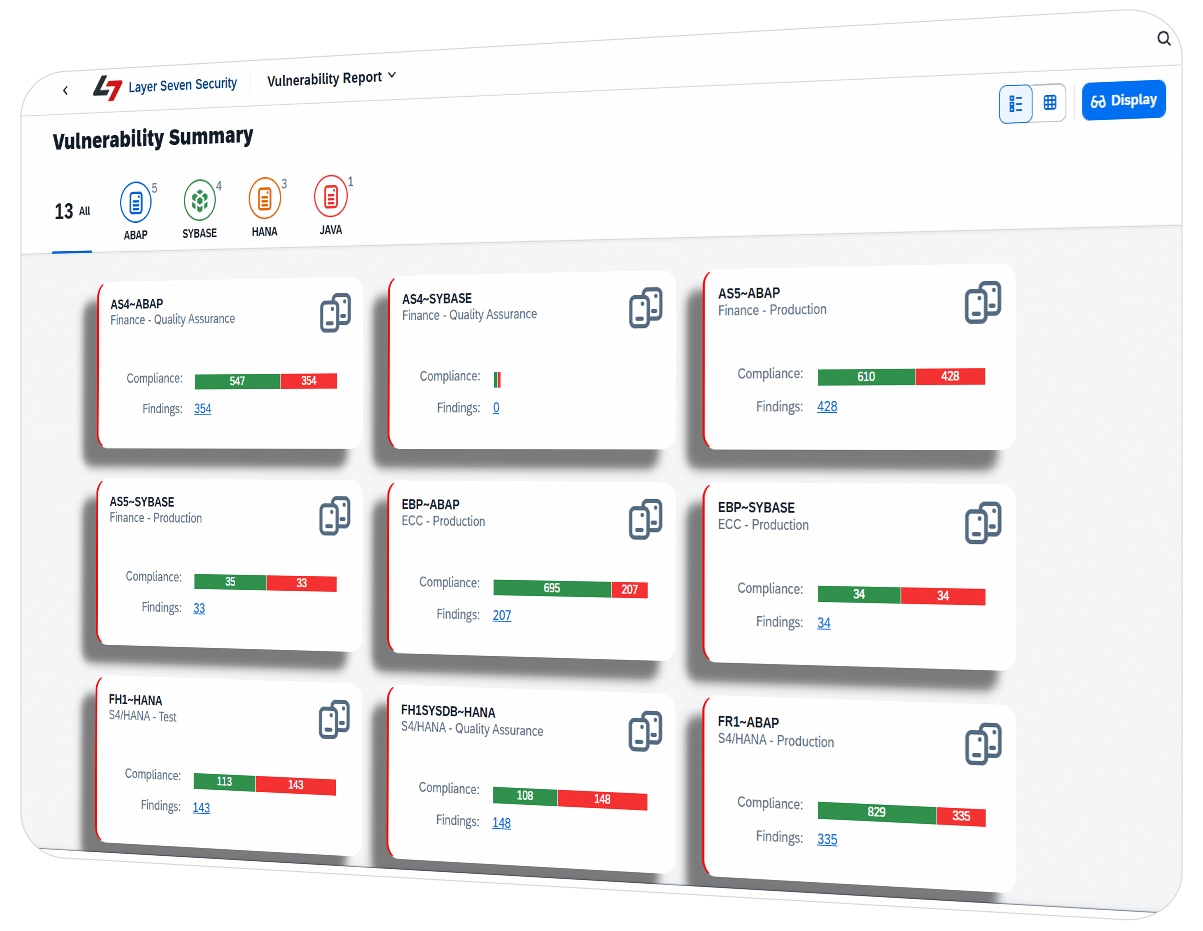
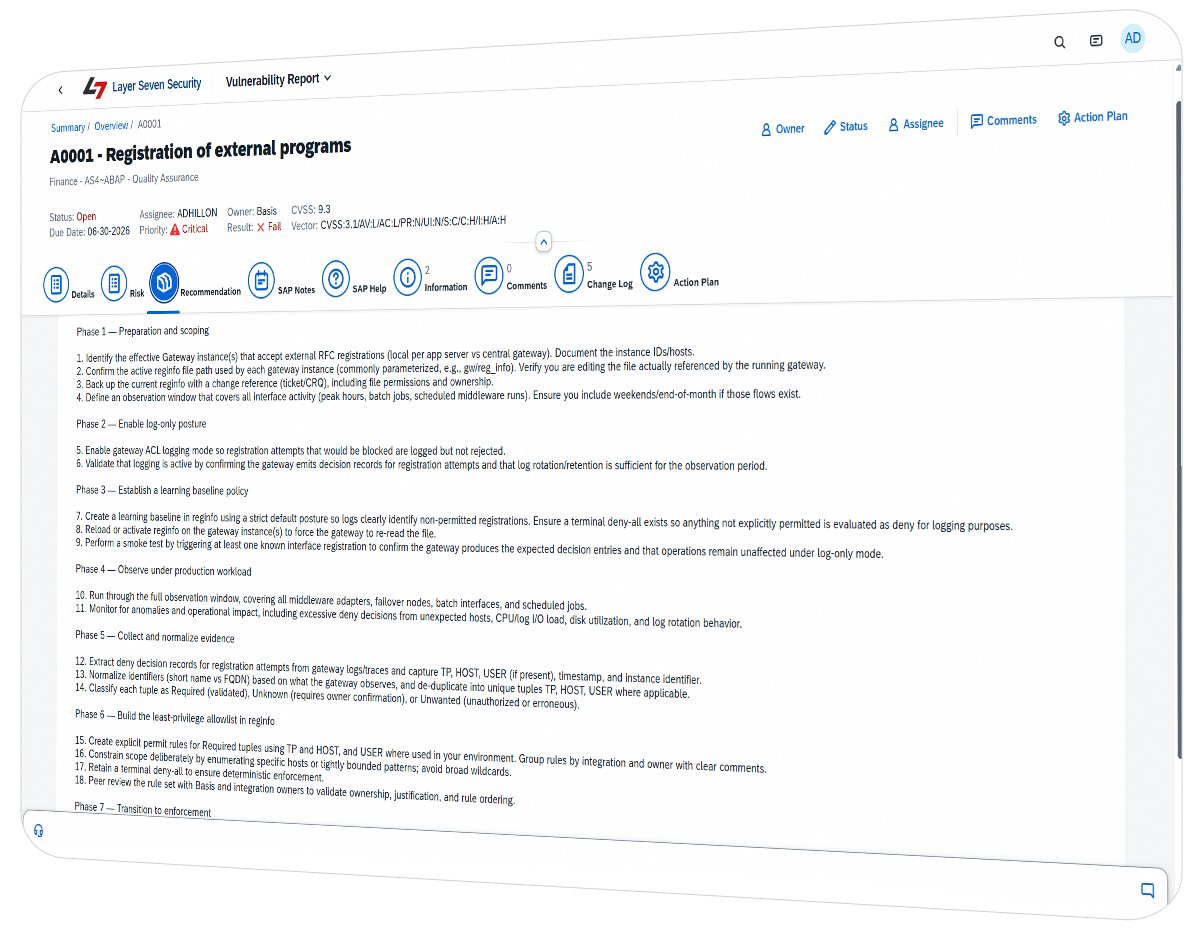
Harden SAP systems against targeted attacks. Secure custom code and discover relevant security notes.
Detect and investigate indicators of compromise using pattern matching and anomaly detection. Integrate alerts with SIEM solutions.
Automate audits for SOX, GDPR, NIST and other frameworks. Comply with mandatory security requirements for SAP RISE & Cloud ERP.
We deliver industry-leading coverage with faster deployment, simpler maintenance, and lower licensing costs.

4.3 / 5
L7S has been, since the demo, phenomenal with their services. They have the kindest and most productive staff you can ask for and not only are they quick and receptive to our requests, but they also deliver through and through. They are exemplary to what we need when it comes to…
– Software Development | Firm size: 10B-30B USD | Industry: Consumer Goods

Your production uptime is non-negotiable. Our SAP Certified status guarantees that the Cybersecurity Extension for SAP meets the rigorous performance, stability, and architectural standards required to run natively within your most critical enterprise systems.
A 360-degree review of your SAP landscape, identifying deep-stack vulnerabilities and mapping Shared Responsibility gaps and mandatory security requirements in your SAP RISE or cloud environment.
Advanced technical testing that goes beyond network ports to find logic-level flaws in your SAP application layer. We simulate real-world attack vectors to reveal the true business impact of a breach.
High-performance scanning of custom ABAP programs and UI5 applications to discover backdoors, code injections, missing authorization checks, and other programming vulnerabilities.
Specialized audits for SAP Cloud ERP environments to identify compliance gaps with mandatory security requirements in SAP RISE.
See Your SAP Blind Spots in Just 6 Hours