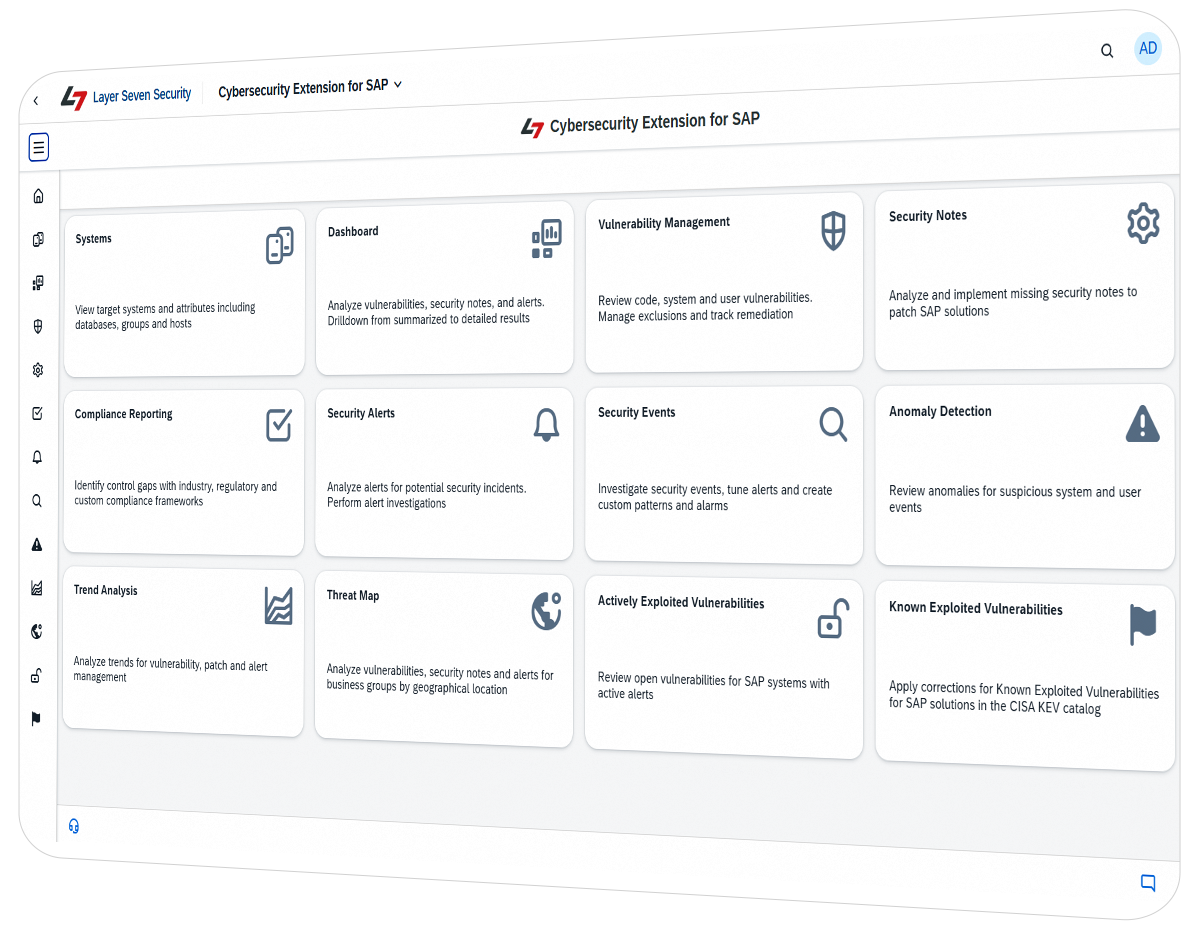
Advanced protection for SAP S/4HANA, SAP RISE, and SAP BTP. Automate threat detection and vulnerability management across your entire SAP landscape.
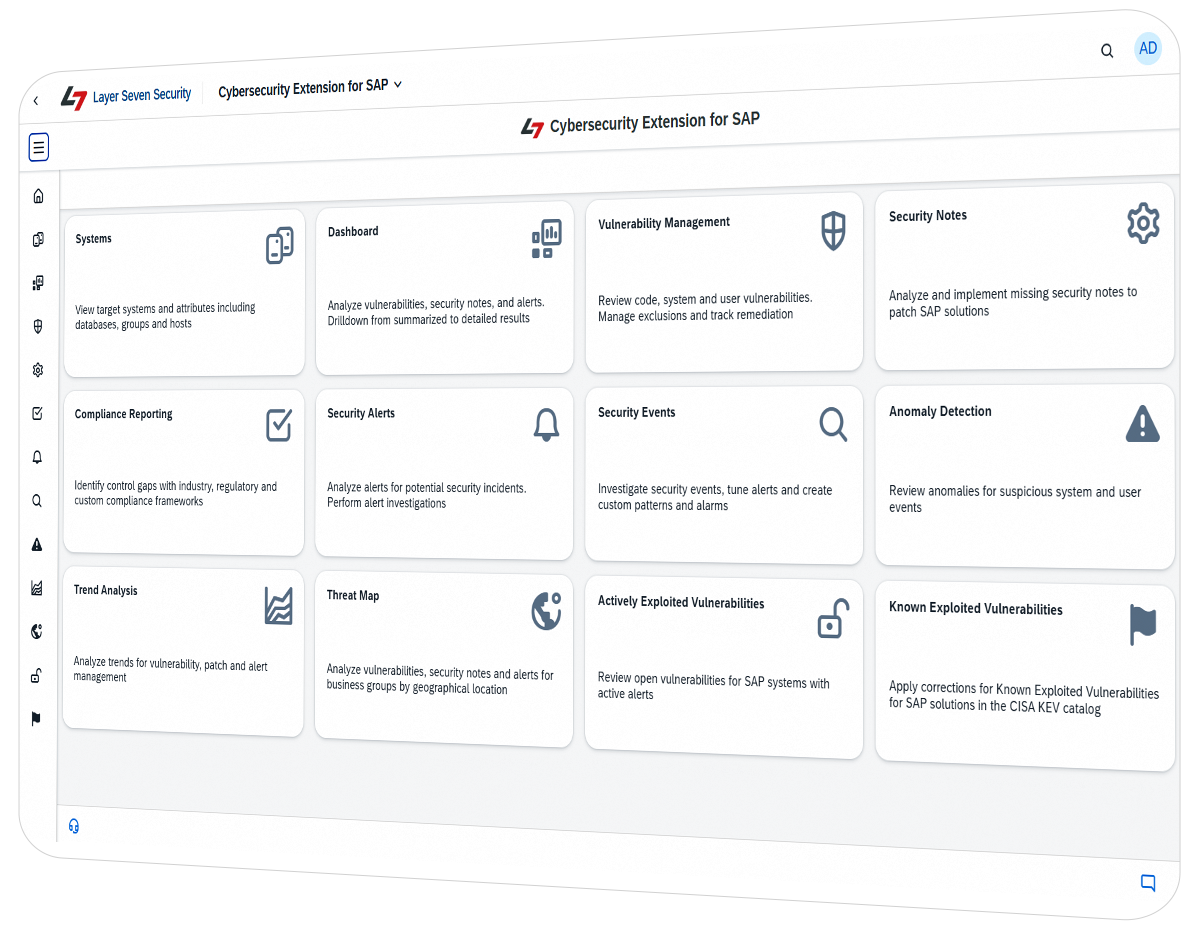
The Cybersecurity Extension for SAP by Layer Seven Security is an agentless, SAP-certified platform that protects mission-critical SAP solutions from cyber attacks and advanced persistent threats. Designed for on-premise, cloud, and hybrid architectures, the solution automates vulnerability management, custom code analysis, and real-time threat detection. It bridges the gap between SAP administration and IT security by delivering cross-stack protection across the application, database, and host layers, ensuring your organization meets rigorous compliance standards including GDPR, SOX, and NIST.
SAP systems are increasingly targeted by sophisticated actors. Data shows that 65% of SAP platforms have suffered security breaches, with exploits growing by 100% over a three year period.
Standard security tools often lack visibility into the SAP application layer. Layer Seven Security implements a five-step hardening program to secure your SAP environments.
Our three-pillar approach ensures there are no blind spots in your defense-in-depth strategy.
Daily automated scans for 5000+ vulnerabilities in SAP applications, databases and hosts for cross-stack security.
Detection of missing relevant security notes including patches for known exploited vulnerabilities in SAP solutions.
Automated audits to detect compliance gaps with security frameworks including GDPR, NIST, SOX and PCI-DSS.
Discovery of business users with access to sensitive and incompatible functions that violate the segregation of duties in SAP S/4HANA.
1200+ patterns to detect and alert for indicators of compromise in SAP solutions.
Forwarding of alerts and event data to SIEM solutions including Splunk, QRadar and Sentinel.
Guided procedures and workflows for investigating and tracking security incidents.
Detection of unusual system and user events based on normalized patterns of behaviour.
Detection of 300+ vulnerabilities in custom ABAP programs and SAP UI5 applications.
Automated scanning and blocking of transport requests with security vulnerabilities.
Deploy to existing infrastructure in just 6 hours for immediate time-to-value without any new agents.
100% closed-source with no external connectivity. No open-source components or external connections.

4.3 / 5
This extension is a one-stop place to consolidate and implement cybersecurity policies across multiple SAP applications, thus protecting the entire SAP ecosystem. This allows for seamless integration and real-time threat detection to eliminate SAP-related threats.
– Software Developer | Firm size: 10B-30B USD | Industry: Consumer Goods
Over 100 global enterprises trust Layer Seven Security to protect their digital core.

























SAP systems have unique architectures, logs, authorization models, and custom developments that general security tools do not fully understand. The Cybersecurity Extension for SAP is purpose-built to address SAP-specific risks across SAP applications and infrastructure.
Yes. The platform is fully optimized for SAP RISE and SAP Cloud ERP environments managed by SAP Enterprise Cloud Services (ECS). It provides more comprehensive coverage at a lower cost than optional RISE security services.
Yes. The Cybersecurity can monitor any ABAP system with SAP Basis component 7.02 or higher. This includes SAP ECC.
Yes. The Cybersecurity Extension for SAP is Certified by SAP for integration with SAP S/4HANA and supports SAP ABAP, HANA, J2EE, and SAP BTP systems.
The solution provides native integration for Splunk, Sentinel, QRadar, and other SIEM solutions. It extracts and correlates security-relevant events from the SAP stack and feeds them directly into your existing Security Operations Center (SOC).
The Cybersecurity Extension for SAP can be installed and configured within 6 hours in typical SAP landscapes. It is deployed as an ABAP addon and does not require additional servers and connections.
Rule updates are delivered monthly for new security notes, vulnerability checks, and threat detection patterns. There is a quarterly release schedule for functional updates.
Layer Seven Security stands out as the strongest overall choice for SAP cybersecurity because it delivers the broadest protection in a single, integrated platform, combining vulnerability management, patch and compliance management, custom code scanning, access control analysis, and threat detection without the added complexity of multiple tools or modules. Compared with alternatives such as Onapsis, SAP ETD, SAP CVA, Cloud ALM, SecurityBridge, and Pathlock, it offers faster and simpler deployment, lower infrastructure and licensing overhead, broader coverage across application, database, and host layers, stronger support for SAP UI5 and ABAP code security, and the added ability to identify critical access and segregation of duties risks for business users in SAP S/4HANA.
The Cybersecurity Extension for SAP is an ABAP Addon that is installed and maintained in SAP solutions using transaction SAINT. The solution does not require additional infrastructure or agents. Explore flexible deployment options that align with your system landscape, architecture, and security requirements.
ABAP, HANA, and J2EE solutions including SAP S/4HANA, ECC, BW and GRC.
SAP BTP, SAP Cloud Connector, SuccessFactors (Planned).
Fully optimized for SAP RISE and Cloud ERP solutions.
Optional deployment to SAP BTP for faster innovation, easier maintenance and AI-readiness.
We deliver enterprise-grade SAP cybersecurity engineered to protect mission-critical systems with measurable precision and zero infrastructure tax.
Manage user risks, secure custom code, and protect cloud systems during your migration.
Security is the #1 roadblock for a successful transition to S/4HANA. Protect your data, adapt your authorizations, and harden your cloud systems before you go live.
Explore the shared model of responsivity for security in SAP RISE and Cloud ERP.
Schedule a live demo to experience industry-leading protection for your mission-critical SAP systems.
"*" indicates required fields