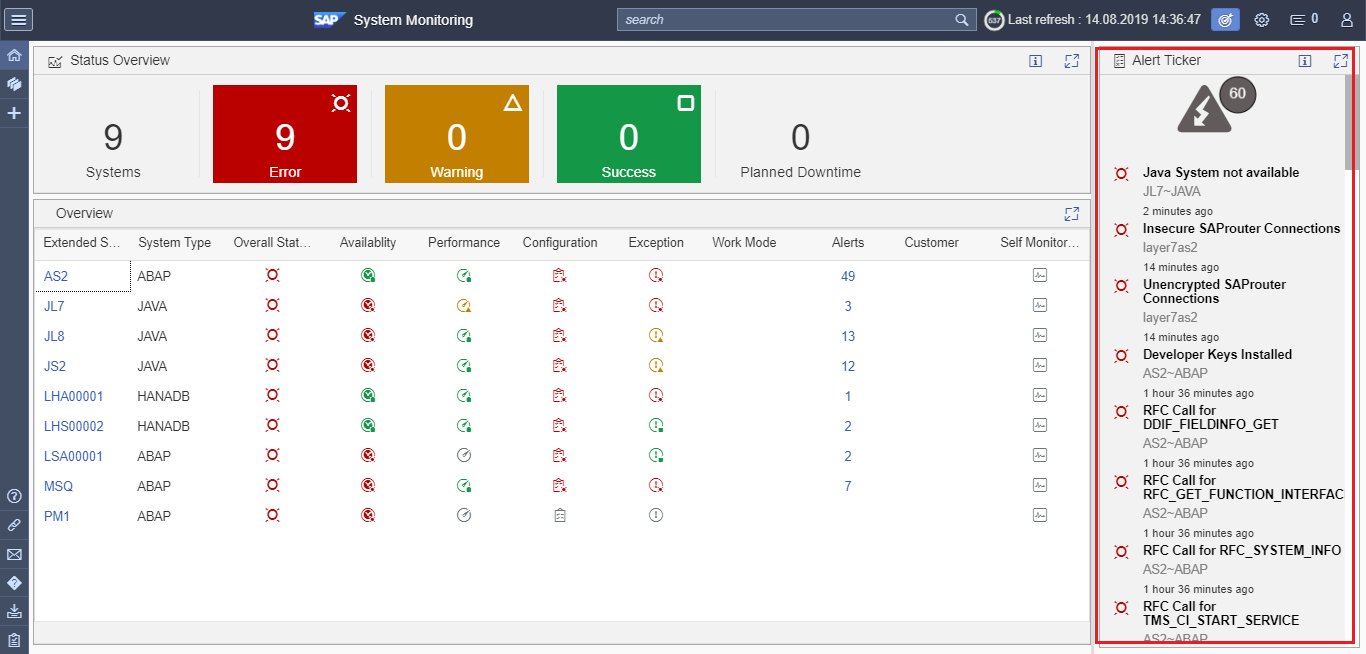
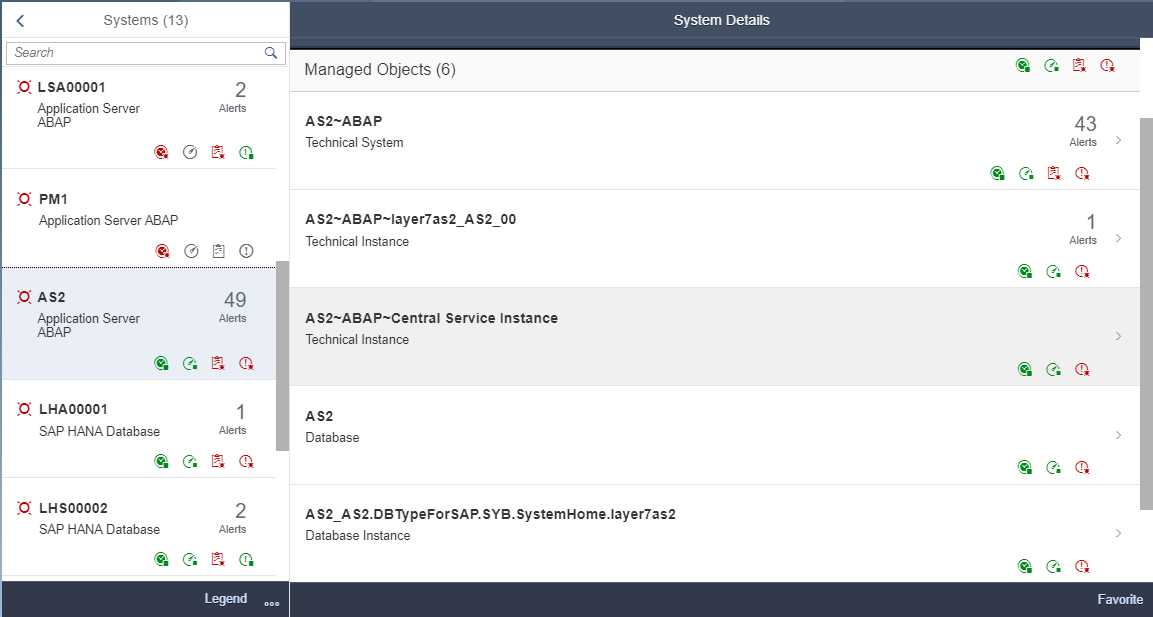
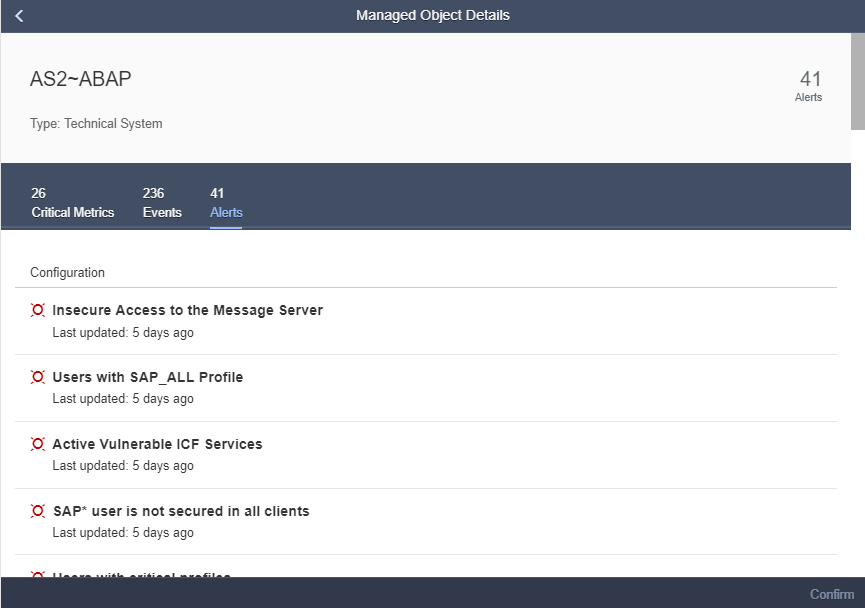
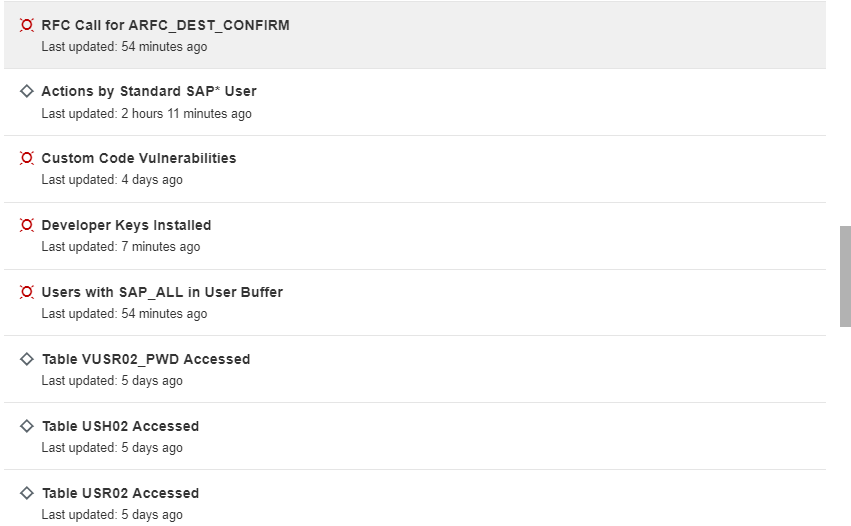
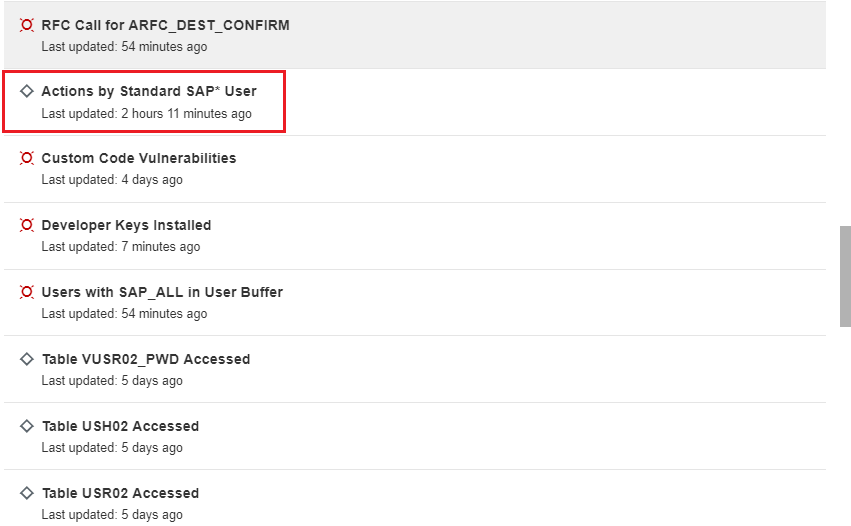
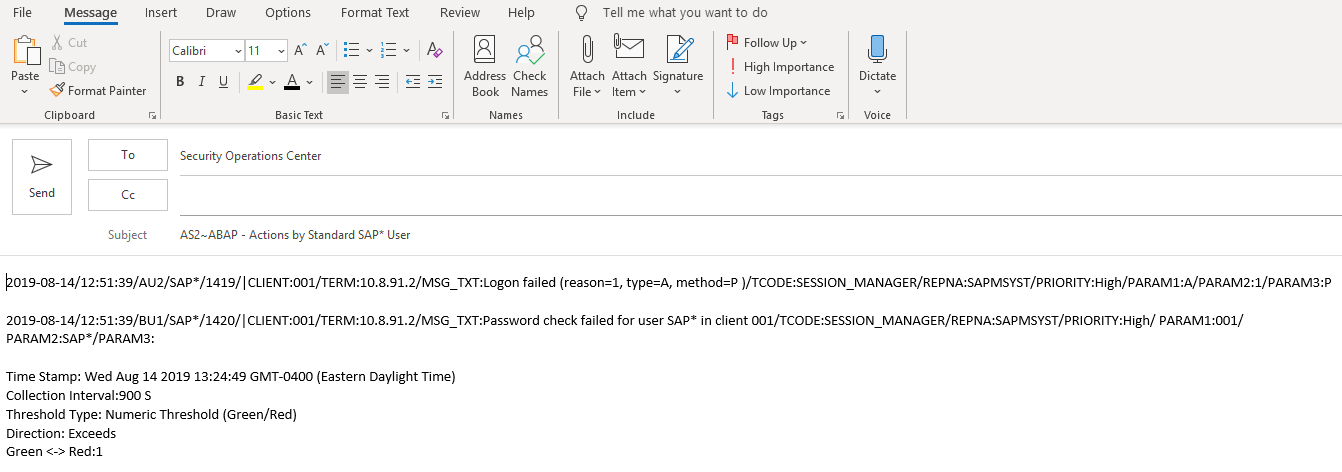
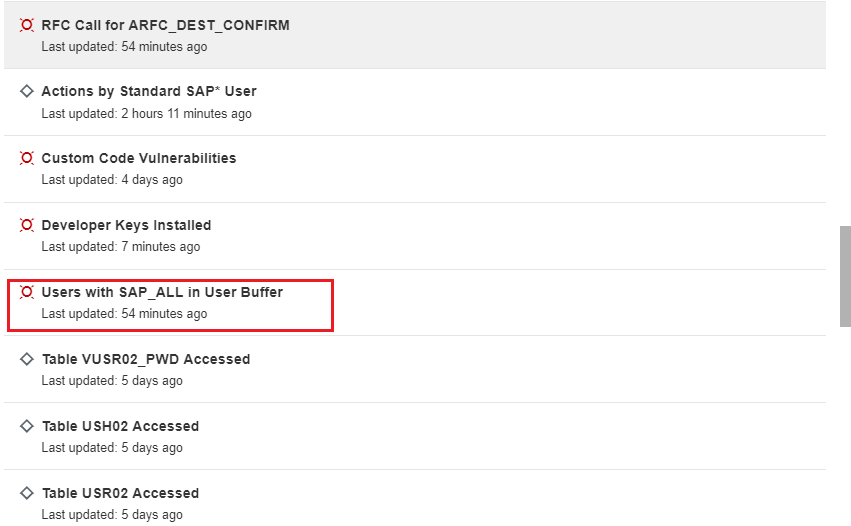
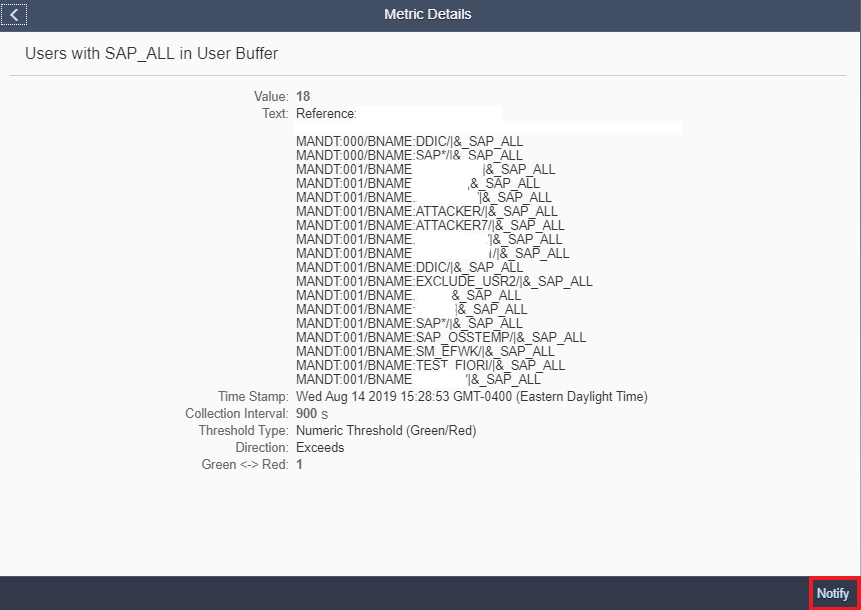
The Cybersecurity Extension for SAP Solution Manager monitors SAP event logs to automatically detect and alert for indicators of compromise. The monitoring interval can be customized for each security metric based on risk and sizing. An interval of 60 seconds, for example, can support real-time threat detection. However, real-time detection is only useful when supported by real-time incident response. Organizations that lack rapid response capabilities should opt for collection intervals of 10-15 minutes to balance the need to minimize the mean to detect (MTTD) with the system impact of continuous monitoring.
Log settings also need to be carefully maintained to capture
security-relevant events while preventing the accumulation of log data and the consumption
of excessive disk or table space. The recommended settings and archiving
procedures below for each log area will enable you to maintain comprehensive
forensic logs with minimal system impact.
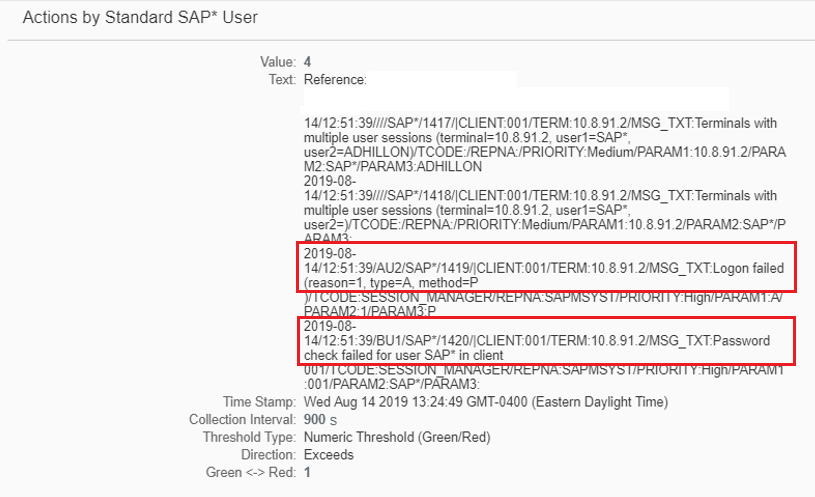
Security Audit Log
Maintain static filters to log all actions by the standard SAP* user, logons and transaction starts by the DDIC user, and Severe and Critical events for all audit classes and users. Also create a static filter to log the non-critical event IDs BU4, CUY, DU9, DUI, and FU1. The filters should be applied to all clients. If you have yet to remove the EarlyWatch client, also create a filter to monitor events for all audit classes and users in client 066.
Periodically export events older than 30 days using
transaction SM20. Once the events are successfully exported and backed-up to a
file server, trigger the background job RSAUPURG to delete events older than 30
days using transaction SM18.
Read Access Log
Configure or import logging purposes to log access to sensitive fields and tables including user tables. Archive SRAL objects using transaction SARA. RAL archives can exported and stored offline.
Change Documents
Change documents for user changes are triggered automatically. Similar to the Read Access Log, change documents are archived using transaction SARA.
Business Transaction Log
There are no specific settings required for STAD. Since data is retained for only 48 hours, STAD archiving is also not required.
System Log
Similarly, the system log does not require any specific settings or archiving. The system log is a ring buffer. When the log file reaches its maximum size, the system overwrites the oldest data.
HTTP Log
The LOGFORMAT option for HTTP logging should specify a format that includes the URL in log entries. An example is the CLF format. HTTP log files in the /usr/sap/SID/instance/work directory can be exported and archived offline.
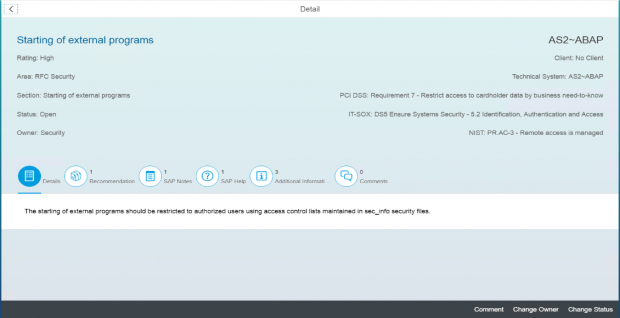
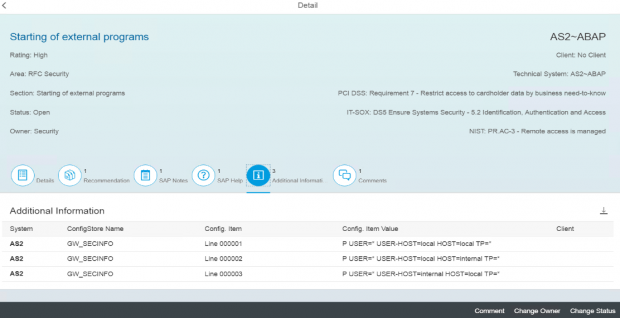
Gateway Server
The ACTION option for gateway logging should include the actions SsZMP to capture security events, configuration changes, and monitor commands. Gateway log files are can also be found in the work directory of each instance and archived to an external location.
Java Security Log
The value of the following properties should be set to TRUE to include the client host address, object name and actor in logged events: ume.logon.security_policy.log_client_hostaddress, ume.secaudit.get_object_name, and ume.secaudit.log_actor. Automatic archiving should be activated using the Log Manager. Once activated, the compressed archives can be found in usr\sap\<SID>\JC<Instance number>\j2ee\cluster\<Dispatcher or server>\log\archive.
HANA Audit Log
The target audit trails should be set to CSTABLE and SYSLOGPROTOCOL to log events simultaneously to internal tables and the OS-level system log. Audit policies should be configured to log critical actions including all actions performed by the SYSTEM user, system changes, user changes, role changes, repository changes, and unsuccessful logons.
The contents of the AUDIT_LOG table can be exported using the AUDIT OPERATOR privilege in the HANA Studio. Once exported, navigate to the Auditing tab in the Security section and select the option to truncate the audit trail.
For detailed step-by-step instructions, refer to the section on Log Settings and Maintenance in the user manual for the Cybersecurity Extension for SAP Solution Manager.