Equifax Data Breach: Attackers Exploited an Unapplied Security Patch, not a Zero-Day Vulnerability
On September 15, Equifax released a statement to confirm the initial attack vector that led to the compromise of personal information relating to 143 million consumers in the US, UK and Canada targeted an Apache Struts vulnerability within a web application that supports the organization’s online dispute portal. The patch for the vulnerability had been available since March but had not been applied by Equifax at the time the breach was detected on July 29. The patch was subsequently applied by Equifax but it was too late – the damage had been done.
Predictably, Equifax’s patching procedures have been cast into doubt with many questioning why the organization took four months to patch an external-facing web application that accessed large-volumes of sensitive information. The doubts were evidently shared by the Board of Directors at Equifax: both the Chief Information Officer and the Chief Security Officer were forced out last week.
Fortunately, few SAP applications are impacted by the Apache Struts vulnerability addressed by CVE-2017-5638. Although many SAP products including Banking, BusinessObjects, and Sybase use the Apache framework, very few products use the Struts library within the framework.
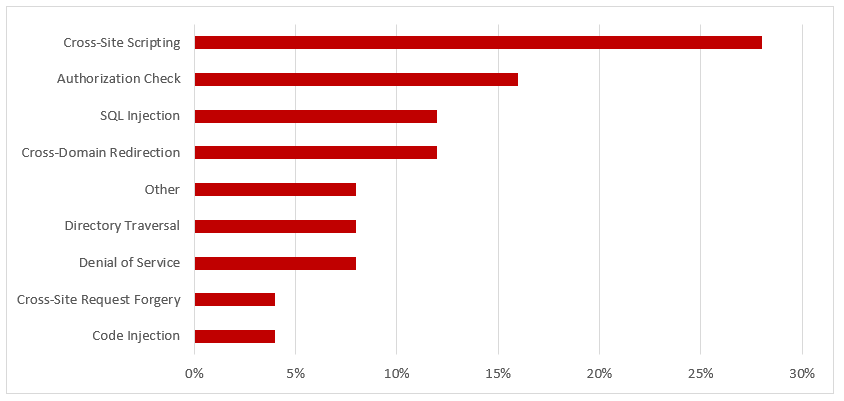
However, SAP customers are strongly advised to review and revise their patching efforts in light of the breach. Despite concerns related to zero-day vulnerabilities, the root cause of the vast majority of breaches remains poor security practices rather than zero-day attacks. This includes ineffective patching procedures that open a wide window of opportunity for attackers to exploit known vulnerabilities before they are patched by organizations. This point was emphasized by a statement from Fortinet with the recent release of the company’s Global Threat Landscape Report. According to Fortinet, “Cybercriminals aren’t breaking into systems using new zero day attacks, they are primarily exploiting already discovered vulnerabilities”.
SAP customers can discover and apply security patches for SAP products using System Recommendations (SysRec). SysRec is an application within SAP Solution Manager that connects directly to SAP Support for real-time patch updates. It also connects directly to each system within SAP landscapes to monitor patch levels. SysRec downloads corrections for security vulnerabilities from SAP Support to each system. It also integrates with other areas in Solution Manager including Usage Logging and Solution Documentation for change impact analysis, Change Request Management (ChaRM) for managing changes, and Test Management for testing and deployment.