The Data Breach Investigations Report (DBIR) has chronicled the growth in security and data breaches for over a decade. The findings of the most recent report released on April 27 are based on the analysis of more than 42,000 security incidents across a variety of industries and countries.
For the first time, the DBIR examines security breaches for key industries to analyze threats confronted by specific verticals. According to the report, attack patterns and motives, as well as susceptibility to different forms of attack vary considerably between industries. For example, manufacturing companies are more likely to fall victim to phishing attacks than public sector organizations. Manufacturers are also more likely to be targeted by attackers motivated by corporate espionage than financial fraud. The industry insights are useful for aligning defense strategies to the risk profiles of each vertical.
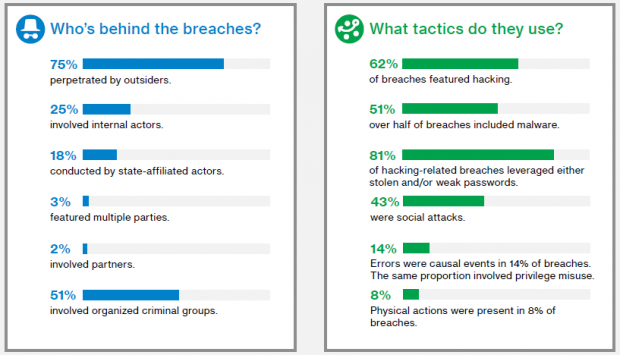
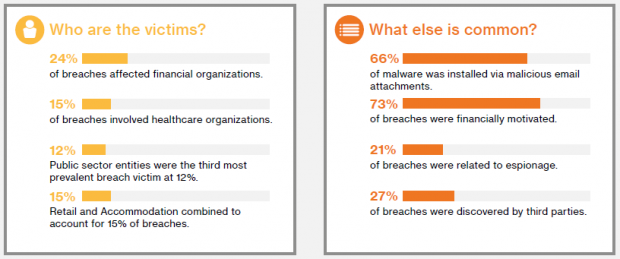
Overall, the DBIR revealed that the majority of breaches (75%) are perpetrated by outsiders. Over half of attacks are performed by organized criminal groups and 18% by state-sponsored attackers. Internal resources are detecting a greater proportion of breaches than prior years, pointing to improving detection and response capabilities within organizations.
Hacking and malware remain the leading causes of security breaches. The report revealed a 50% increase in ransomware attacks. Ransomware is now the fifth most common form of malware, up from 22nd in 2014. There was also a noticeable increase in phishing attacks. Phishing is used in 21% of security incidents and has a success rate of 7.3%.
The DBIR analyzed patching processes across industries and concluded that most sectors follow a quarterly patch cycle. However, the percentage of patches implemented on-time varies from a high of 97.5% in the Information sector to a low of 18% in Education.
The findings of the DBIR are summarized below. The full report is available at Verizon Enterprise.