Anomaly Detection with Cybersecurity Extension for SAP
Threat detection is commonly performed through rules or signature-based pattern matching. Detection engines compare actual events with patterns of malicious events to discover indicators of compromise (IOCs). IOCs discovered by detection engines typically trigger an alarm or alert for a suspected security breach.
Pattern matching is a tried and tested method to identify known exploits in systems including SAP applications. However, there are several drawbacks with the approach. Attackers can obfuscate their actions to bypass attack detection patterns. Also, since pattern matching detects IOCs based on known signatures, new or emerging IOCs that have not yet been registered are not detected.
Anomaly-based threat detection provides an alternative to pattern matching with greater protection against anti-forensics and the capability to detect previously unknown attacks. Anomaly-based systems rely on profiles of expected or normal user and system behavior. Actions by users or events in systems that deviate from the profiles generate an alarm or alert.
Unlike rules and signatures for patten matching, profiles for anomaly detection cannot be created and maintained manually. Anomaly detection is usually applied through machine learning platforms that automate profile building and analysis for large pools of data.
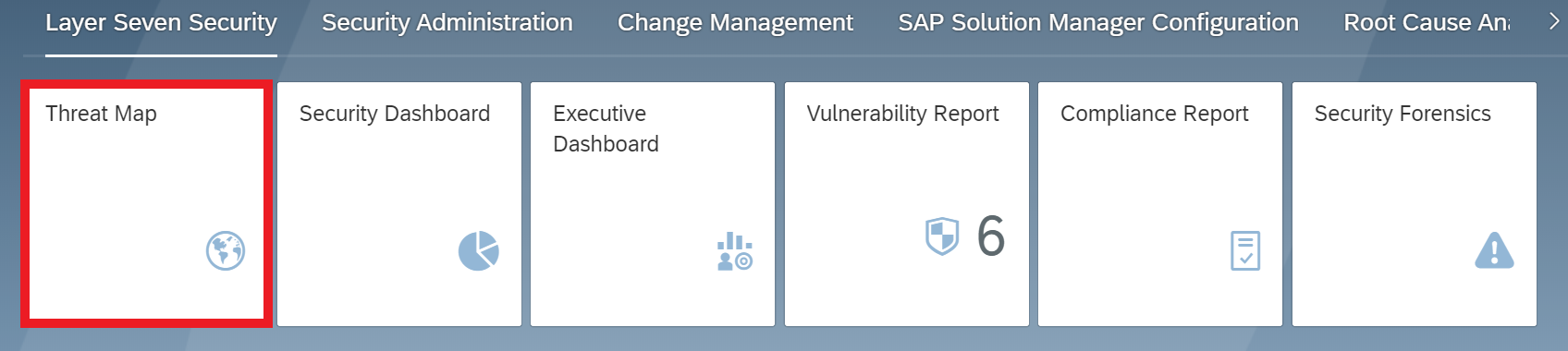
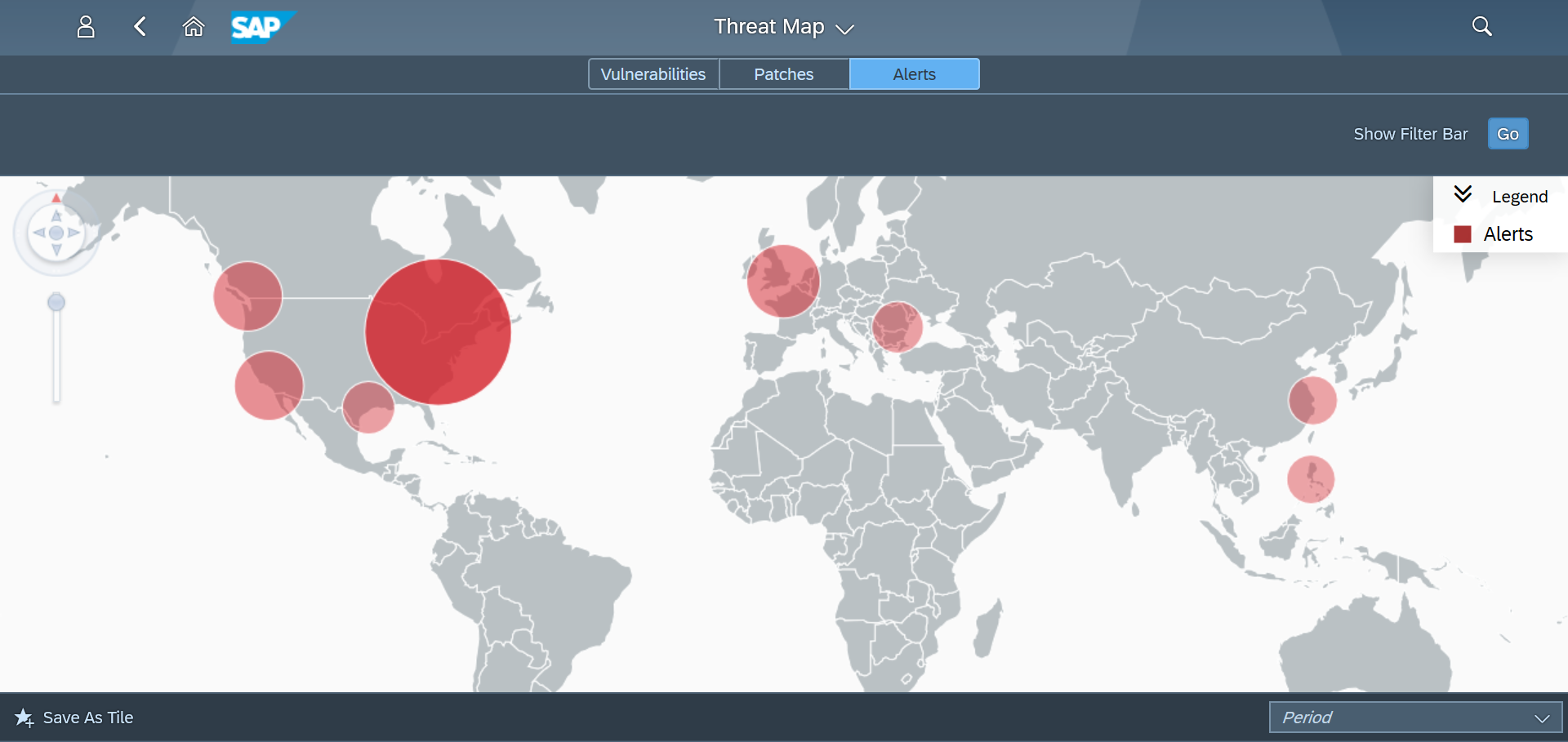
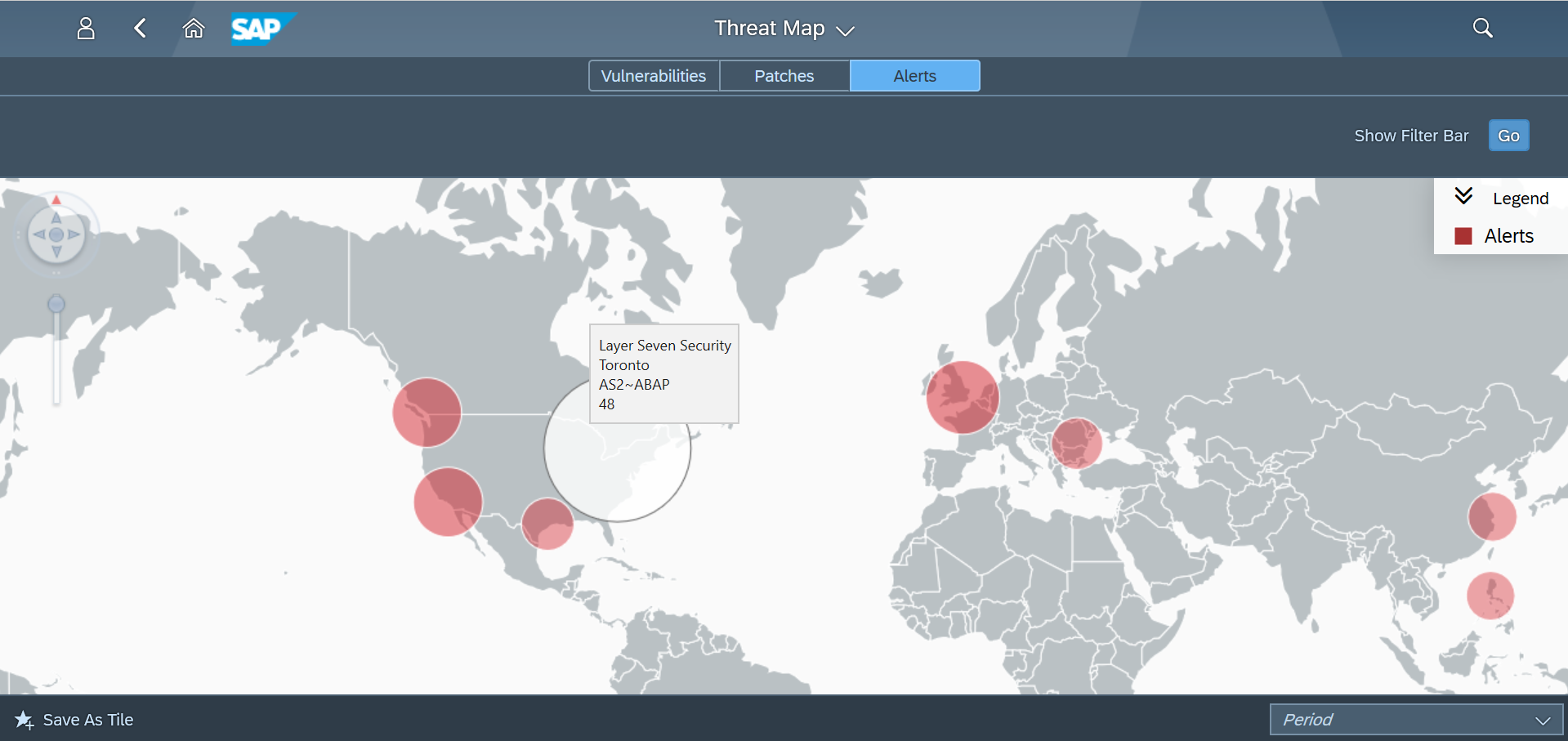
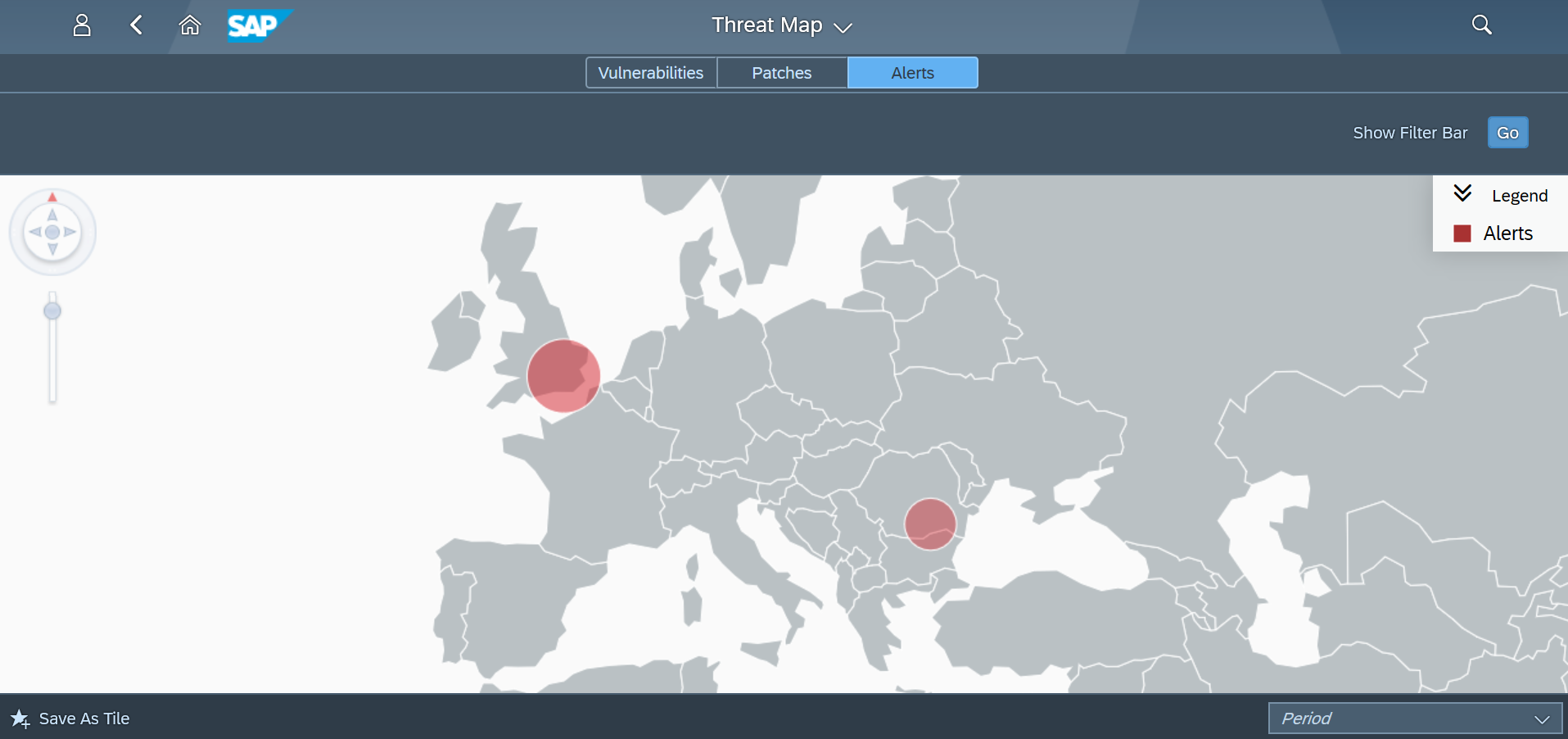
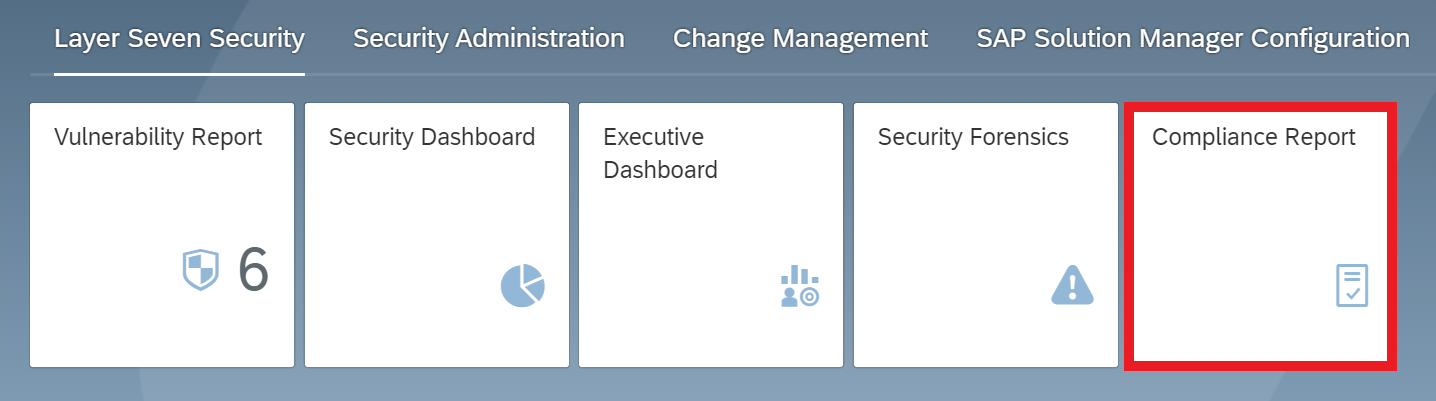
The Cybersecurity Extension for SAP uses a pattern matching approach for threat detection in SAP systems. IOCs detected by the solution using pattern matching are displayed and managed in applications such as Security Forensics, System Monitoring, and the Alert Inbox. For anomaly detection, event logs collected, filtered, and normalized by Solution Manager are forwarded to the Predictive Analysis Library (PAL) in SAP HANA.
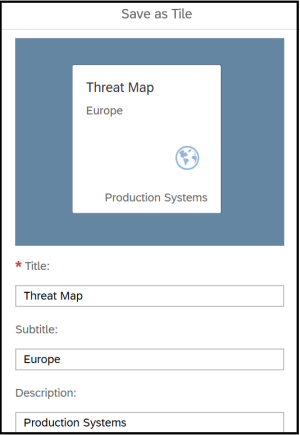
PAL includes functions for applying complex analytic algorithms using SQLScript database procedures. The functions include procedures for clustering, regression, time series, and other algorithms that are used to detect outliers in security logs. Anomalies discovered by PAL are transmitted back from SAP HANA to the Anomaly Detection app in the Cybersecurity Extension for SAP. The application is accessed from the Fiori launchpad in SAP Solution Manager.
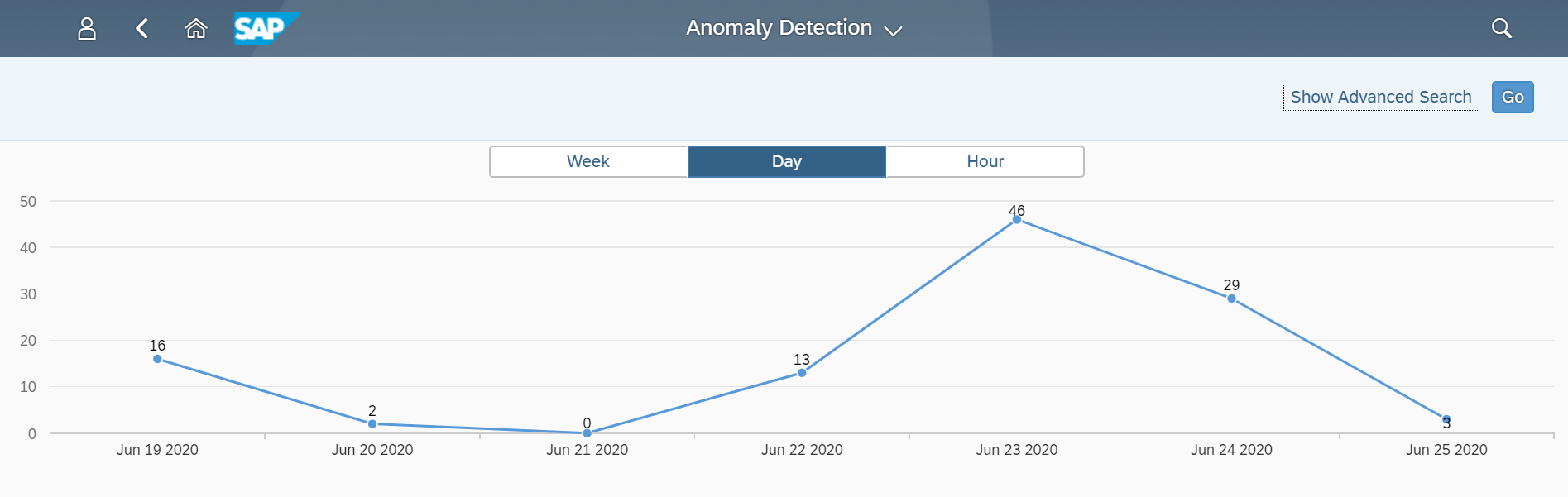
Anomaly results are summarized by period. Results can be analyzed by the week, day or hour.
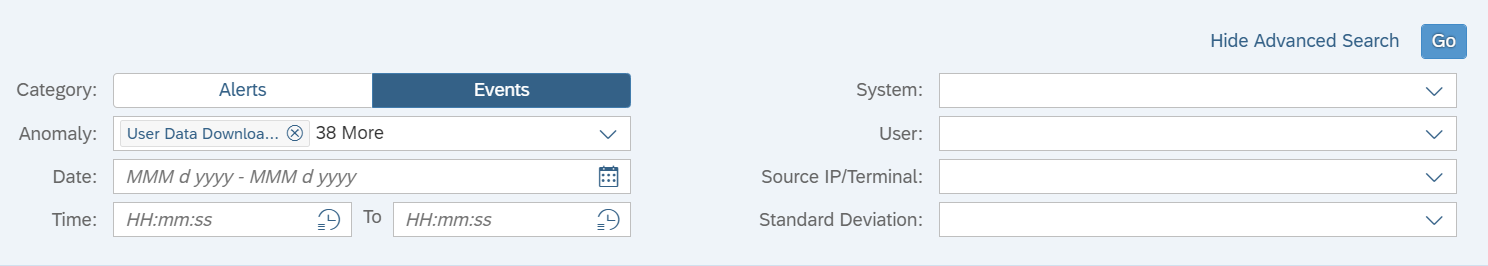
Results are filtered using Advanced Search. This supports filtering by anomaly, date, time, system, user, and source IP/ terminal. Results can also be filtered by anomaly type to view anomalies based on either event data or alert data. Event anomalies include outliers such as high volume of transaction starts, report starts, or data downloads, or a user request from a new IP address or terminal. Alert anomalies include areas such as high volume of alerts for a specific system, user or source, or a new alert for a user or system.
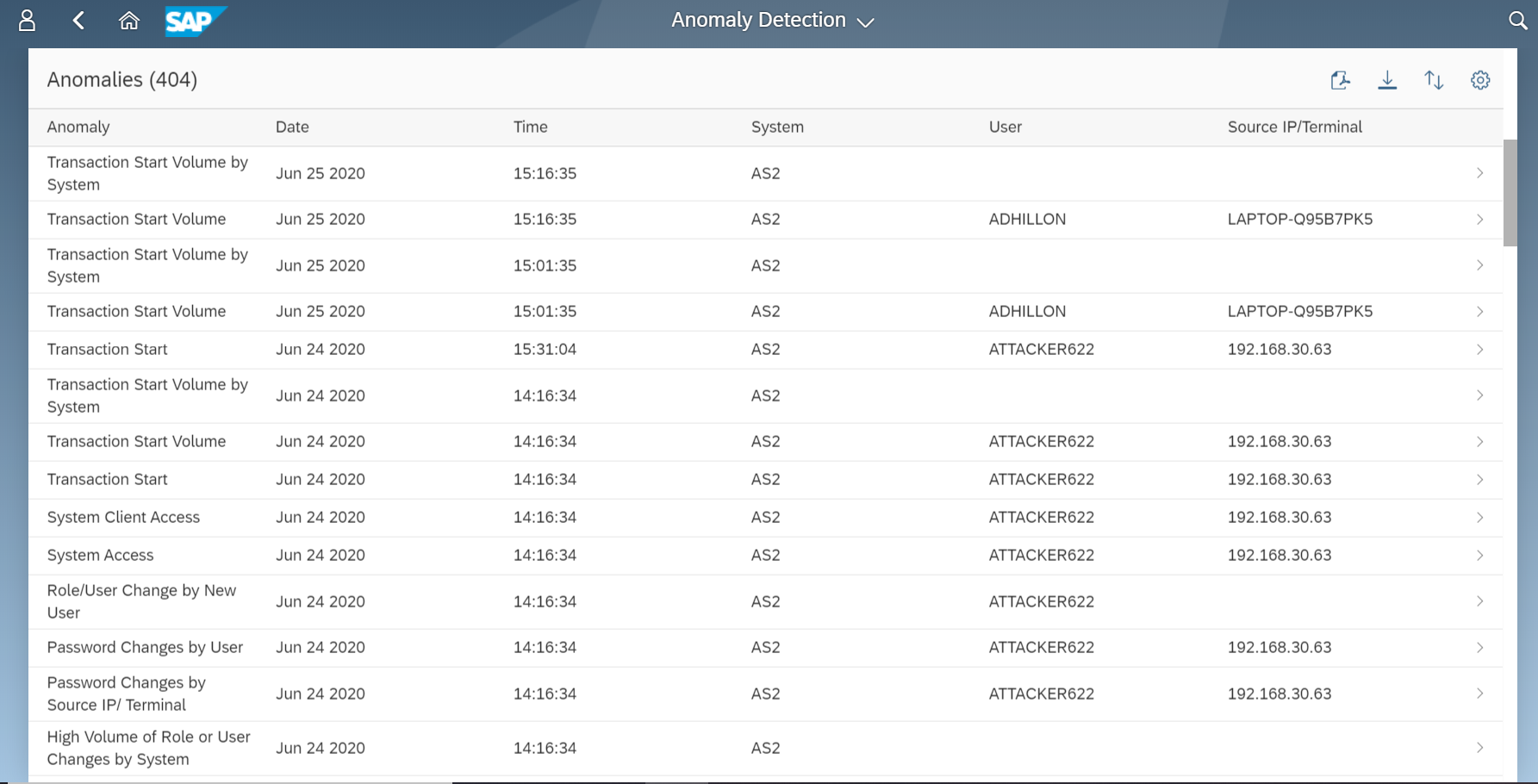
Anomalies calculated using standard deviation are scored based on distances from statistical averages. The further the distance from the mean, the higher the confidence level for the anomaly. The results displayed in Anomaly Detection are prefiltered for medium and high confidence anomalies. Anomaly-based threat detection can have a higher incidence of false positives than pattern-based detection. It can generate alarms for every deviation from expected norms. Therefore, an effective scoring mechanism is essential to enable security administrators to identify and focus on high-confidence anomalies.
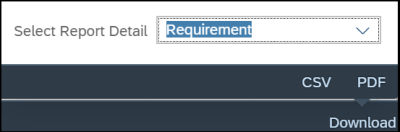
Results can be sorted and exported to CSV/ PDF with the applied filters. The layout can be personalized by users to add, remove, and rearrange columns.
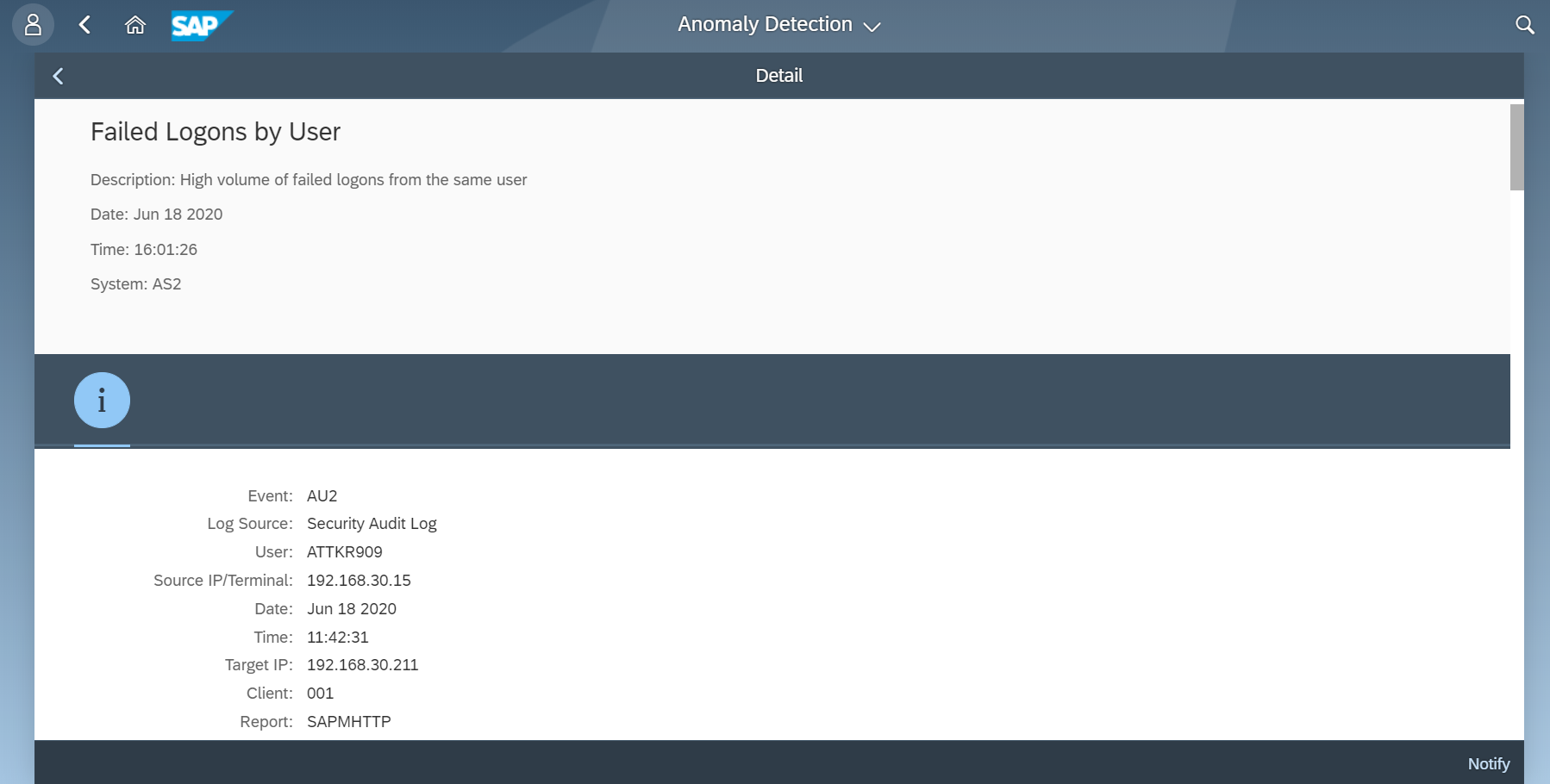
The details for each anomaly can be viewed by clicking on an anomaly in the summary. Anomaly times are in UTC. Timestamps for events are based on system time.
The Notify option can be used to append the anomaly details to an email for sharing.
The Cybersecurity Extension for SAP enables advanced threat detection for SAP systems by combining the benefits of both signature and pattern-based detection with anomaly detection using SAP HANA. Licensing for SAP HANA is included with the usage rights for SAP Solution Manager 7.2.