Cybersecurity Extension for SAP Identifies Signatures of Active SAP Cyberattacks
Earlier this month, SAP issued a joint report with a security research firm to highlight active cyber threats targeting SAP applications. According to the report, there is conclusive evidence that attackers are actively targeting and exploiting unsecured SAP applications. The report also reveals that some SAP vulnerabilities are being weaponized in less than 72 hours from the release of SAP patches. Unprotected cloud installations of SAP are being discovered and compromised in less than 3 hours.
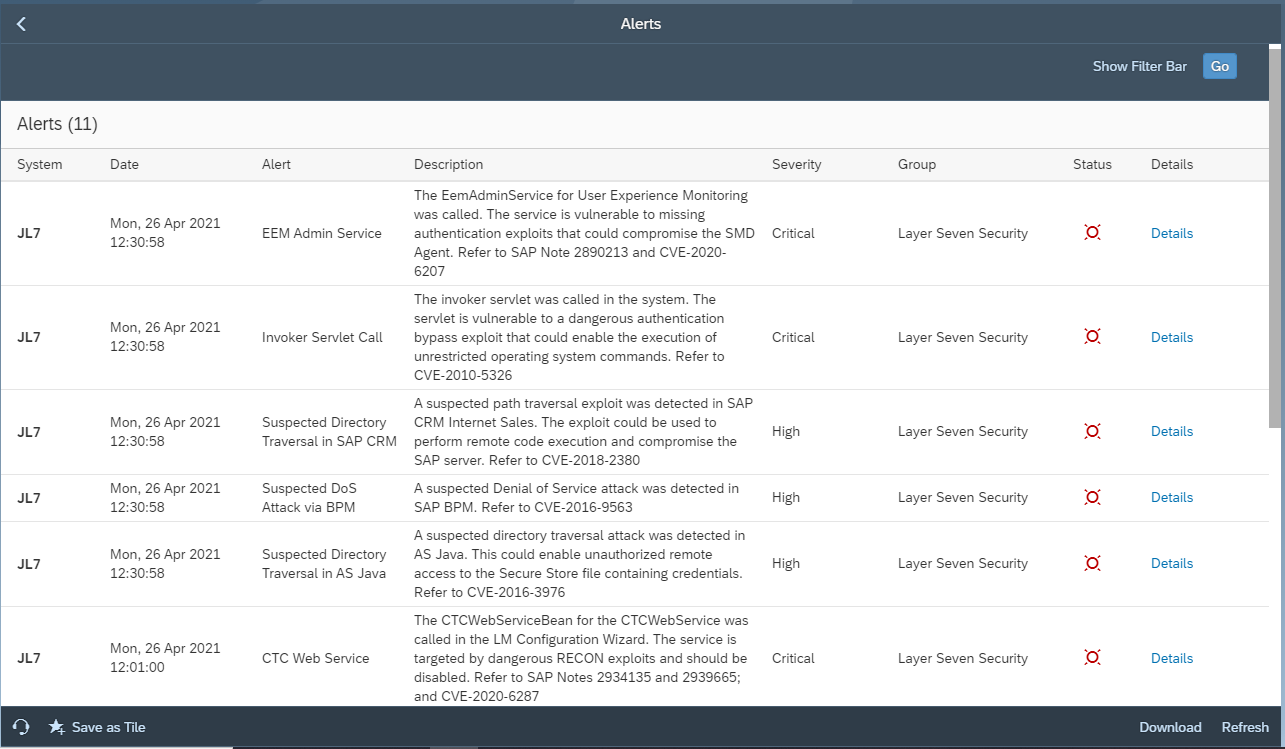
The investigation performed for the report identified over 300 successful exploitations of SAP systems. This included attempts to modify users and configurations and exfiltrate business information. Most of the exploits targeted the six CVEs below. Although the vulnerabilities have been patched by SAP, many organizations have not applied the recommended mitigations to protect SAP systems.
CVE-2010-5326 (SAP Security Note 1445998)
CVE-2018-2380 (SAP Security Note 2547431)
CVE-2016-3976 (SAP Security Note 2234971)
CVE-2016-9563 (SAP Security Note 2296909)
CVE-2020-6287 (SAP Security Note 2934135)
CVE-2020-6207 (SAP Security Note 2890213)
SAP recommends customers to immediately assess vulnerable systems to identify indicators of compromise such as unauthorized privileged users. The assessment should include systems within SAP landscapes that are connected to the vulnerable targets. The related SAP security notes and recommendations should also be applied in impacted systems.
SAP also urges customers to implement appropriate cybersecurity measures to protect SAP applications. The Cybersecurity Extension for SAP is an SAP-certified solution that performs automated vulnerability management, threat detection and incident response to secure SAP systems from cyber threats. This includes exploits that target the CVEs highlighted in the report. The Extension detects misconfigured and unpatched systems. It also detects the signatures of exploits that target the CVEs, triggers alerts and notifications for suspected breaches, and provides guided procedures for investigating incidents. To learn more, contact Layer Seven Security.