Turn the Tide against Cyber Attacks with SAP Enterprise Threat Detection
One of the most striking facts revealed by the 2014 Verizon DBIR is that only one in every six data breaches are detected by organizations that are the victim of such breaches. The statistic revealed that the vast majority of organizations lack the capability to detect incidents that lead to a data breach.
According to an earlier study sponsored by Oracle, organizations that have implemented incident detection capabilities are not necessarily any better off: nearly 70 percent require greater than one day to identify incidents of unauthorized system access. Given that most breaches unfold in less than a single day, organizations could suffer catastrophic losses before they even detect the underlying incident.
The problem is particularly acute for SAP environments. Maintaining a low mean time to detection is one of the key metrics used to measure the effectiveness of threat management programs. This is the gap between the time an incident occurs and the time the threat is detected and contained. While SAP systems generate a large quantity of logs in various formats, collating and parsing such logs presents several technical challenges, as well as consuming an extensive amount of time and resources. Performing such an analysis in near real-time using conventional tools is impractical, especially in high-volume environments that often generate several gigabytes of log data each hour. Hence, means times to detection are generally high for threat management programs encompassing SAP systems. This increases the vulnerability of such systems by providing adversaries with a longer timeframe to attack and compromise systems before detection.
Under these circumstances, the general availability of SAP Enterprise Threat Detection (ETD) on March 16 could not have been timelier. ETD is the only solution capable of providing visibility into potential insider and outsider threats impacting SAP systems in real-time. ETD minimizes mean times to detection and therefore shortens the timeframe that adversaries are provided to compromise and harm systems. It does so by harnessing the data streaming capabilities of the Event Stream Processor (ESP) and the ability of SAP HANA to analyze large and complex data sets instantaneously.
Log data is automatically extracted from monitored systems and components and pushed to a REST-based API exposed by ESP. Log information is harvested from a wide array of sources within each system including Gateway, HTTP, Business Transaction, Change Document, Read Access, System, Security Audit and User Change Logs. ETD SP01 also supports logs that use the UDP-based syslog protocol. Syslog is a common standard for capturing, labelling and transmitting system events for security auditing and other purposes. It is used by a wide variety of systems and components including, most notably, SAP HANA or, more specifically, the SUSE platform supporting HANA.
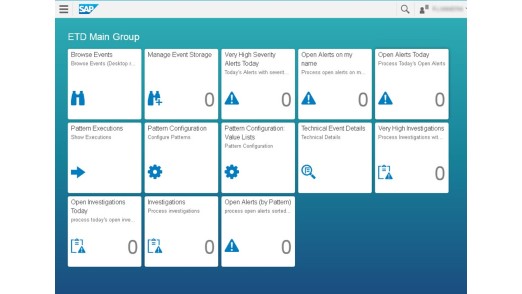
Once the log data is formatted and normalized by ESP, it is transferred to SAP HANA for storage and made available to ETD for analysis. Threat detection using ETD is performed primarily through pattern recognition. In other words, log data is evaluated by ETD to determine whether logged events match predetermined patterns for suspicious activity. Examples include logon attempts using standard users, multiple and concurrent failed logon attempts in the same system using the identical user, or changes to variables implemented during a debugging session. Patterns are risk-weighted by severity and trigger an alert whenever a match is detected by ETD. Alerts can be viewed through the ETD Dashboard or Launch Pad (see below).
ETD SP01 includes over 50 patterns for ABAP systems based on SAP best practices. However, SAP recommends enabling and tuning patterns to address specific risks within each landscape and developing custom patterns using the Pattern Configuration tool bundled in ETD. Pattern identification and development is also performed by SAP Service Partners such as Layer Seven Security.
Future releases and enhancements of ETD will widen support for Java and cloud-based systems. SAP also intends to integrate ETD with Solution Manager for monitoring and incident management.
SAP ETD closes a critical gap exposed by limitations in existing SIEM and other solutions to absorb and analyze security-relevant event information stored in SAP logs. It also delivers the capability to identify and respond to security threats revealed by event data in real-time. For these reasons, ETD represents one of the most important technological innovations in SAP security in recent years and offers the most effective response to insider and outsider threats impacting SAP systems.
The use-cases for ETD can be illustrated by the recent insider breach at AT&T that led directly to a $25M FCC fine levied against AT&T. The breach centered on the accessing of personally-identifiable customer information by call center employees without authorization. This information was subsequently sold by the employees to third parties. Such a scenario can be mitigated in SAP systems through the integration of Read Access Logs with ETD. Providing the relevant patterns are appropriately configured, ETD would generate an alert when sensitive data fields are accessed by users frequently and in large volumes. Since the alert is generated as the incident is unfolding, it will provide investigators with the opportunity to respond to the incident in real-time and prevent the leakage of sensitive data.
To learn more about Enterprise Threat Detection, you can visit SAP at booth #S216 in the South Expo Hall at the upcoming RSA Conference. You can also contact Layer Seven Security.