Monitoring the SAProuter with SAP Solution Manager
The SAProuter performs a pivotal role in SAP landscapes by filtering SAP traffic using a more granular approach than is possible with conventional network-level firewalls. As a stand-alone program, it is commonly installed in DMZ servers that support network services rather than SAP applications.
The SAProuter is often targeted by attackers given it’s function as the gateway to SAP systems. There are several attack vectors targeting known vulnerabilities in earlier versions of the program. Therefore, it’s important to regularly update the SAProuter to the latest release and patch level. You can refer to note 1897597 for release information and note 1921693 for instructions for updating the program. Other recommendations include changing the well-known default port and blocking remote access to the SAProuter. This could be abused to control the SAProuter from external clients or hosts. It can also be exploited to modify the route permission table.
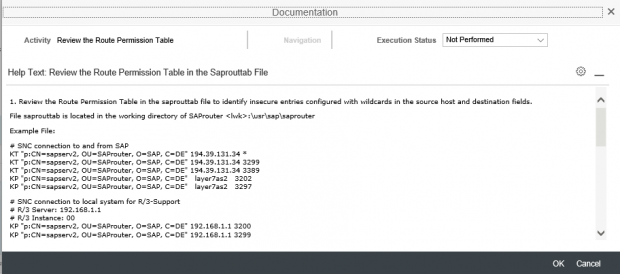
The route permission table is maintained in the saprouttab file stored in the working directory of the SAProuter and controls route strings between hosts. It applies an access control list to permit or reject connections between source and target systems through the SAProuter. Standard entries in the route permission table have the syntax P (Permit) /S (Secure) /D (Deny) <source-host> <destination-host> <destination-port or service> <password>. The password option for permitted connections is optional.
The access control list should be as restrictive as possible and only permit the necessary connections. Wildcards (*) should not be used in the destination host and port fields. The rule D * * * * should be included as the last entry in the list to explicitly deny all connections that are not defined in the route permission table.
Lastly, the access list should be configured to support only authenticated and encrypted connections using the K prefix for positive entries. This requires the configuration of Secure Network Communications (SNC) for the SAProuter. For detailed instructions, refer to the SAP guide for SAProuter SNC Configuration.
The SAProuter can be monitored with SAP Solution Manager. The Solution Manager Diagnostics (SMD) agent should be installed on the server hosting the SAProuter. The Remote OS Script Collector (ROSCC) is also required to run OS commands through the Monitoring and Alerting Infrastructure (MAI) of Solution Manager. The next steps are the registration of the SAProuter in Solution Manager and the execution of the steps for managed system setup. Once completed, the SAProuter is available for monitoring.
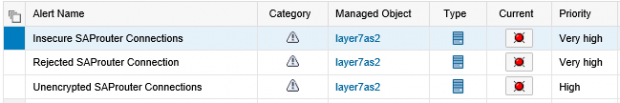
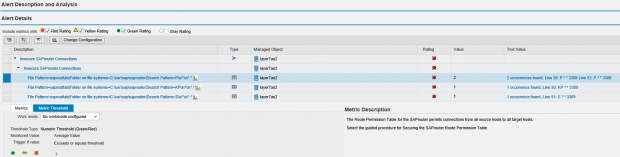
The route permission table can be monitored by Solution Manager to automatically detect insecure entries including unauthenticated and unencrypted connections and entries with wildcards in the destination and port fields. An example is provided below.
The release and patch level of the SAProuter can be checked using the ROSCC. The port used by the SAProuter and whether the program accepts commands from remote hosts can also be monitored with the ROSCC.
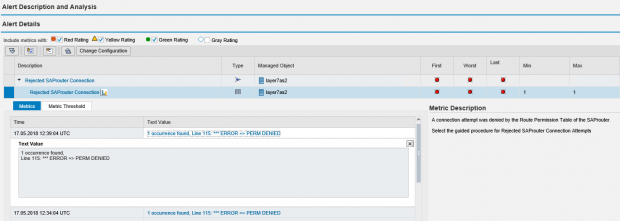
The SAProuter log can be read to detect connections rejected by the SAProuter based on the route permission table. An example of an alert is provided below. Click on the image to enlarge.
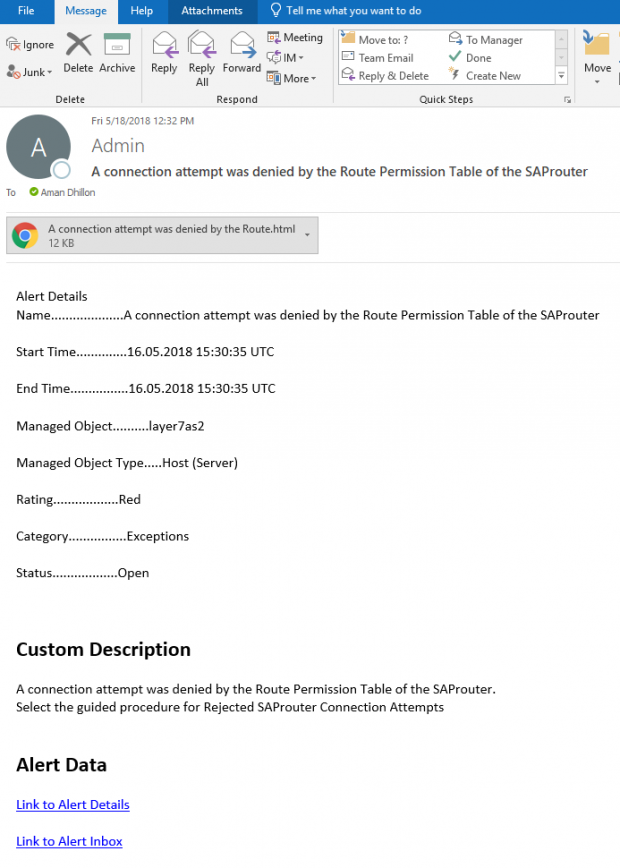
Email notifications are automatically triggered by Solution Manager for alerts. See below.
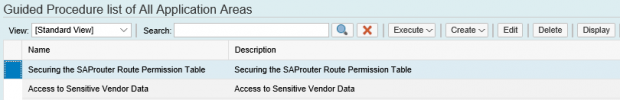
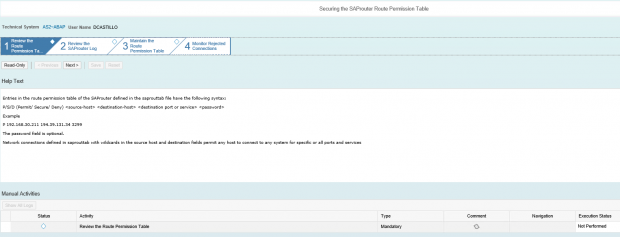
Analysts can execute guided procedures in Solution Manager to investigate alerts and document findings. An example is provided below for Securing the Route Permission Table.
The guided procedure provides a framework for discovering insecure entries in the saprouttab file, identifying required entries, maintaining the route permission table and finally, monitoring the SAProuter log for rejected connections.
Detailed reference documentation is included for each step in the procedure.