How to Visualize Cyber Security Risks in Your Systems with SAP Lumira
SAP Lumira can be used to access, visualize and explore data of any size from virtually any source. It enables users to build and share powerful interactive data visualizations using a simple user-friendly interface. Since Lumira can acquire data and enable users to create customized reports through self-service, it removes the need for programming, scripting and any other form of development.
This article demonstrates how you can use Lumira to visualize security vulnerabilities in your SAP systems and overcome limitations with standard Business Warehouse (BW) reports. The demonstration is based on the Standard Edition of Lumira, available at the SAP Store. This edition will operate with minimal hardware requirements from any system with a Windows 7 or higher operating system.
After Lumira is installed, you will need to add the BW data connector using the Extension Manager since the data source is underlying BW reports in Solution Manager (SolMan). The reports store the results of automated security reviews performed by SolMan. The next step is to set the connection to the BW server in SolMan under Network in the Preferences section. This includes the server URL, hostname, instance and user credentials required for the connection.
Once the connection is established, you can define the variables including reference systems, comparison systems, stores, items and fields. This covers the security policies setup in SolMan, the systems that are mapped for monitoring, and the containers that store the results of the security reviews. We recommend creating a separate Lumira report for each security policy based on different system types (ABAP, Java, HANA, etc.).
You can begin building your visualization and exploring security vulnerabilities as soon as the data is acquired by Lumira. In the report below, we have created charts and tables that convey security vulnerabilities discovered using SolMan by area, system and risk level.
The results can be filtered by any of these elements. The tables provide details of each finding including the objectives of every check, recommendations to remove vulnerabilities, links to relevant SAP Security Notes, and information available at the SAP Help Portal. The reports can be exported to PDF, CSV or Excel. They can also be shared via URLs with users or groups defined in Lumira.
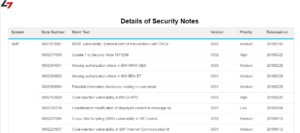
SAP Lumira can be used to visualize not only security vulnerabilities discovered by Solution Manager but also unapplied Security Notes in SAP systems. See below.
To learn more or to discuss how we can assist your organization leverage the full capabilities of SAP Lumira for dynamic, cost-effective and real-time security monitoring, contact Layer Seven Security.